You should stay away from five dangerous extensions, including Netflix Party, according to McAfee.
The purpose of Google Chrome extensions is to simplify your life. Downloading an extension might be highly alluring when there are Chrome browser add-ons that can help you obtain discounts, edit your grammar, take screenshots, and watch shows with others. Malicious extensions, however, imitate the appearance of well-known ones in order to compromise your privacy.
According to a McAfee blog post published on Monday, malicious extensions send users to phishing websites and save affiliate IDs in eCommerce sites’ cookies. According to the security firm, the extensions track users’ browsing habits and send information about each website visitor to servers run by the extension’s developer.
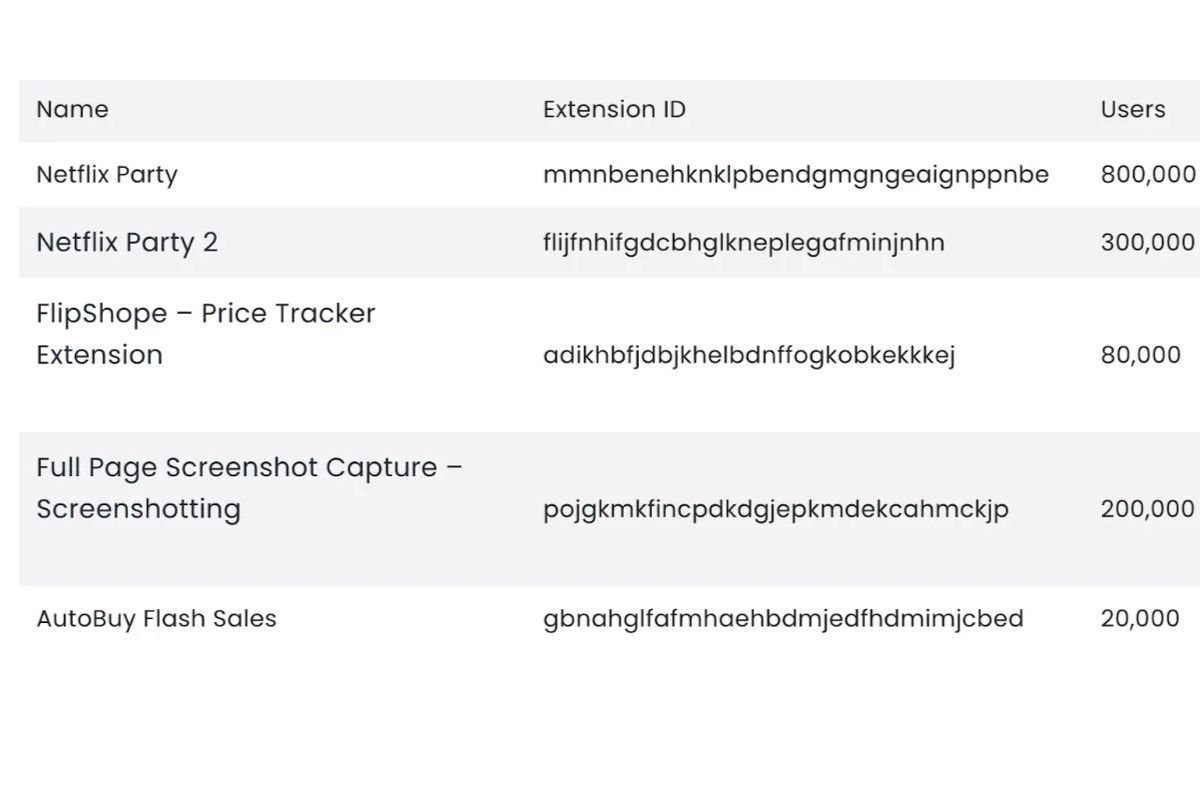
Threat analysts found five Google Chrome malicious extensions that steal track users’ browsing activity. Collectively, the extensions have been downloaded more then 1.4 million times.
Source: https://t.co/TA3K5C3zeH#chrome #cybernews pic.twitter.com/da1bvPeEvJ— P.K. Sharma (@pk_sharma88) August 30, 2022
The designer of the plugin can then add code to the user’s visited eCommerce websites and earn affiliate commissions on any goods the user purchases. When browsing information is disclosed, the consumer’s implicit right to privacy is violated.
The five malicious extensions that McAfee found had a combined install base of over 1.4 million users. They were Netflix Party, Netflix Party 2, FlipShope – Price Tracker Extension, Full Page Screenshot Capture – Screenshotting, and AutoBuy Flash Sales. The list below includes the specific extension names and extension code IDs.
The best defense against exposure is caution while adding Chrome extensions. Additionally, McAfee advises users to carefully read the permission requests that Chrome displays prior to installing the extension. Before providing any rights, users should take extra precautions to confirm the extension’s legitimacy.